AirJack is a popular free-to-download Wifi Hacking tool based on 802.11 version wifi device drivers and it is also known as packet injection tool, which is used for wifi air packet interception and hacking. The tool is designed to work with Linux hardware or a prism network card. Air jack is available with many other names such as WLAN jack and kracker jack. In the beginning, the tool was developed to design wireless applications and drivers in order to transmit the packets for testing purposes. But these days this is the basic tool which is used for different types of attacks such as DOS and man-in-the-middle attack.
Contents
What is AirJack WiFi Hacking Tool?
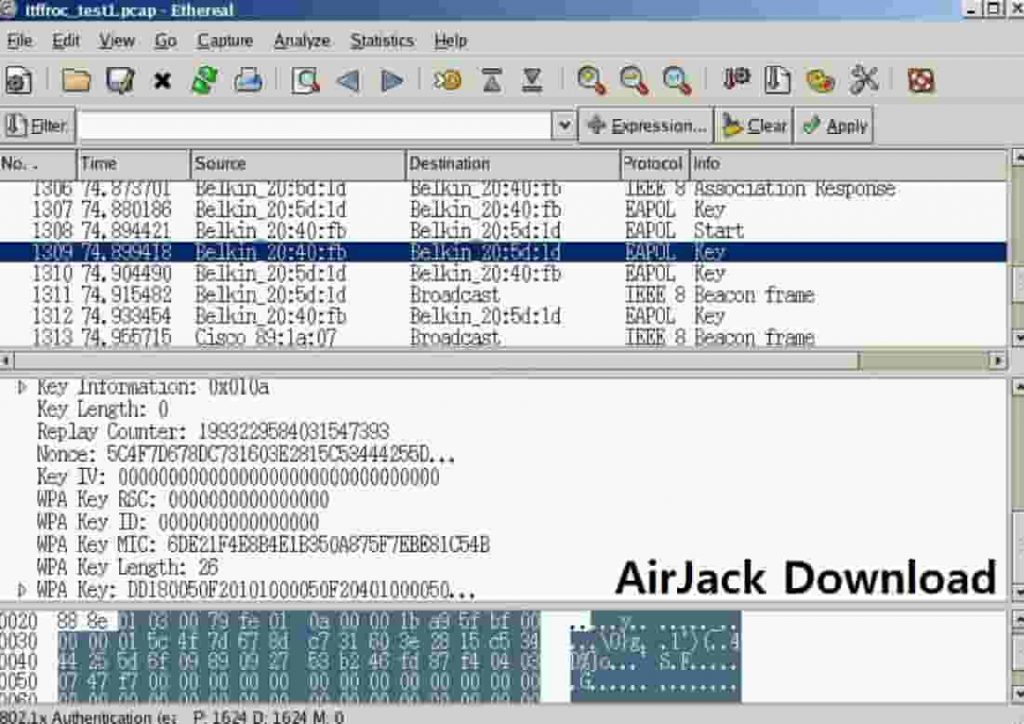
By using this tool hackers can easily inject data packets between the two nodes on any given wireless network. One of the most commonly used features of this tool is to disconnect every user connected to an access point and you know what you can keep them disconnected as long as you wish to. If there is no layer-1 and the target machine is running this tool would easily be able to assume the identity of any other machine on a given network.
Usually, it is done by copying the mac address of the target machine. Once the attacker has obtained the mac address of the target router, it will be able to directly communicate node and ap. The attacker machine will send an unlimited number of de-authenticate frames or packets to the target pc. The network card of the target machine will assume as if the deauthentication packets are being sent by the access point itself and it will disconnect itself from the network. It is a very basic level flaw in wireless network technology.
Read: 11 Best Android WiFi Hacking Apps that are Free (2020).
Can you Hack Wifi Networks with AirJack?
Now you must be wondering why a hacker would send deauthencation packets? Just to disconnect users from a wifi network? Well, it is a little more complicated than that. Sometimes intruders just do it for fun that is just to annoy their neighbors or the target user. But the primary purpose of such an attack is to hack the wifi password. What happens when a user tries to connect with an access point? When a device tries to connect the AP and the device exchange an initial handshake. Hackers try to capture this initial handshake to get to the actual password.
This initial handshake is encrypted, but it is the first step to hack the password or key. In the second step, hackers try to crack it by using a brute force attack. now the question is how you can stop someone from sending the deauthentication packets? To be serious you can’t do much about it or you can say there is nothing you can do about it. Alternatively, you can use vulnerabilities like PMKID to hack wifi network passwords in 2020.
AirJack Features and Overview
You can’t really stop someone from sending data packets in the air. You can’t trace his location and there is no security measure you can take to avoid it. All you can do is to make sure your security key is really long so the hackers couldn’t crack it, even if they manage to capture a handshake. Remember Air jack doesn’t serve this sole purpose of reauthentication there are many other features which are quite useful for the hackers.
Airjack acts as a device driver to perform all the features discussed above it supports all three versions of wifi framework that is a/b/g. its ability to work with all different type of drivers makes it a lethal tool for hackers and script kiddies. Don’t forget the support for air jack has been suspended recently. But there is a ton of free support available online.
Read: Wireshark Free Download Latest Version (2022).
Download AirJack For Free (2022) – Packet Injection Tool
You can easily download AirJack for free and use it. This tool is so popular that it has been downloaded thousands of times. It is definitely a must-have tool, especially if you are into wifi hacking. This tool is the first step towards wifi hacking. You can also use different frameworks like Metasploit Project when it comes to hacking wireless networks.
Now one thing remembers always, download such software from a reliable source, just to make sure that you don’t land yourself in some trouble. Usually unreliable sources, in fact, such software with malicious codes which may be doing their job from your computer and IP address. Be careful while using this tool and remember the information provided here is for educational purposes only and we will not be liable for any misuse.






